QuerySurge Compliance Deep Dive
Automating data validation, enforcing integrity controls, and generating unalterable evidence for SOX, HIPAA, FedRAMP, and ISO audits.
1. Core Architecture & Data Integrity Automation
QuerySurge sits between your data sources and target systems, executing automated, high-speed validation rules. It confirms that every byte extracted, transformed, and loaded (ETL) matches expected outcomes, ensuring absolute data integrity before it reaches critical BI reports or regulatory submissions.
💾
Source Data
Databases
Flat Files
APIs
Mainframes
⚙️
QuerySurge Engine
✔ Schema Validation
✔ Data Type Verification
✔ Row Count Verification
✔ Cell-Level Value Checks
📊
Target System
Data Warehouses
Data Lakes
BI Dashboards
4. Privacy Compliance: HIPAA, GDPR, CCPA
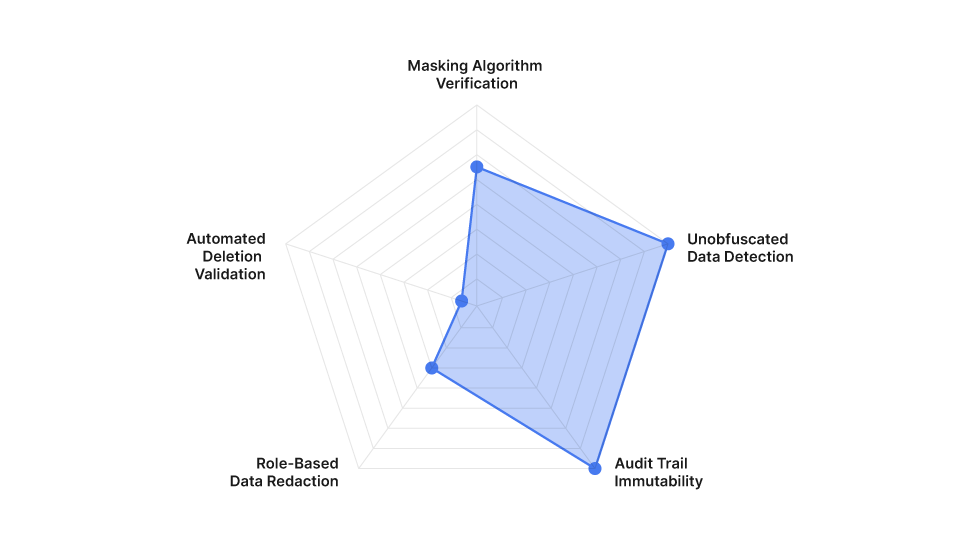
Handling Personally Identifiable Information (PII) and Protected Health Information (PHI) requires robust verification. QuerySurge validates that data masking algorithms are applied correctly during ETL processes, ensuring sensitive data is obfuscated before landing in lower environments.
5. Federal Standards (FedRAMP & FISMA)
For government-regulated cloud environments, QuerySurge supports stringent security baselines required by FedRAMP and FISMA through encrypted communications, secure deployments, and comprehensive system documentation.
🔒
Data at Rest Encryption
Database encryption using AES-256 standards.
🌐
Data in Transit
TLS 1.2/1.3 enforcement across all API and web traffic.
📋
Audit Logging
Immutable system event and execution logs.
📄
SSP Support
Readily available architecture docs for System Security Plans.
6. ISO 9001 & 27001 Validation
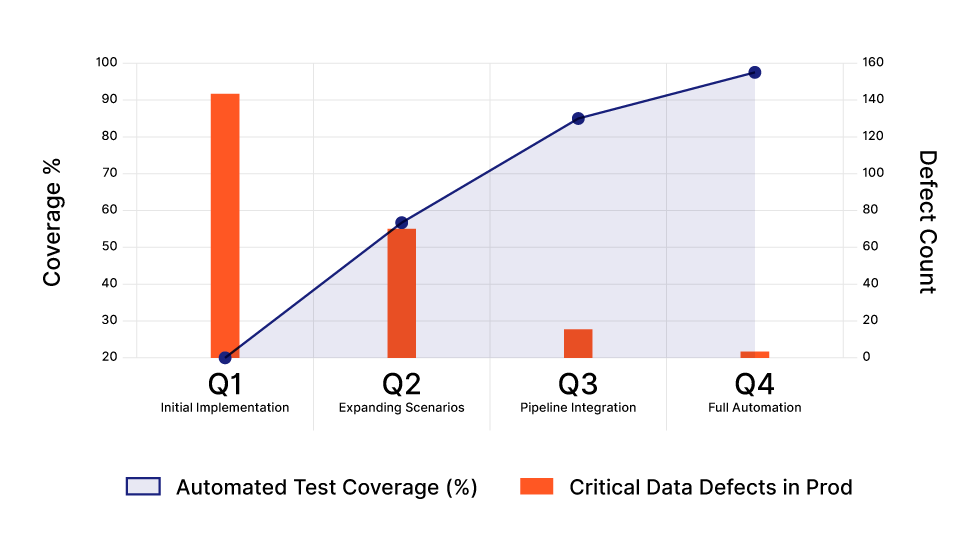
ISO 9001 demands Quality Management and continuous improvement. ISO 27001 requires strict information security. This chart illustrates how increasing QuerySurge automated test coverage directly reduces production data defects over time.
7. FDA 21 CFR Part 11
For Life Sciences, electronic records must be trustworthy and equivalent to paper records. QuerySurge ensures compliance through strict electronic signatures and unalterable audit trails.
- User Authentication
Secure login required before any test design or execution begins. - Test Execution Snapshot
System captures precise timestamp, user ID, and SQL/rules executed. - Unalterable Results Generation
Results (Pass/Fail, Data Snippets) are written to a secure, read-only database structure. - Audit Report Export
PDFs/XMLs generated with cryptographic hashes for auditor submission.